In recent years, we have seen continual growth in the range of cloud systems available and the functionalities that they offer alongside a worldwide shift towards increased remote working practices, which has been somewhat expedited by C-19. This has meant more and more companies are moving towards using and implementing cloud accounting solutions to assist with a wide-ranging set of tasks and functions as well as to enable them to adapt to remote working. This increased reliance on cloud-based products has raised questions within many businesses around keeping data secure and ensuring business continuity can be maintained in various scenarios. Even going back to the “.com” bubble in the late 90s, there has always been a little trepidation around the internet, cloud apps and placing large elements of your business in the cloud rather than on a server that you can see and lock away in a padlocked cupboard.
It is true that, historically, working with a server-based approach provided slightly more guarantees around the security of your systems. With this approach, a person needs to connect to a local server to access your data; therefore, a potential criminal would need to obtain an authenticated laptop, enter the specific local password and username, and connect to your domain to access your folders. If you were in the cloud then theoretically a person could access your data from any laptop if they had the correct web address and could guess the correct username and password. Certain providers do, of course, have mechanisms in place to detect where logins occur and raise warnings or block access if your account is accessed from an unknown location, but this does not necessarily exist across all systems. In truth, the answer to “How safe and secure is cloud accounting?” or indeed any cloud system, depends on how you set your systems up and/or the provider you select. Below, we discuss some measures that we use to ensure our clients are safe and secure when operating in the cloud.
1. Passwords and Authentication:
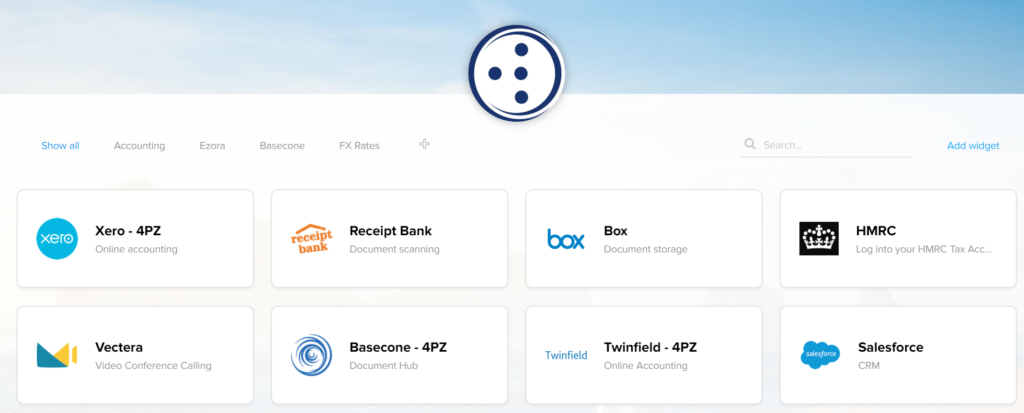
The first and most basic solution is a secure password. Most people will have seen the Barclays adverts on the TV at the moment where they suggest using a combination of 3 unrelated words. Some cloud systems have built-in requirements to use capitals, letters, numbers, and/or special characters when setting your password, all of which will be effective in increasing security. However, we go a step further when asking our clients to access our systems as we always require a complex set-up of characters. It’s important to achieve a balance between making things easy to use and access and keeping things secure. As such, we operate with a secure single sign-on platform so users are only required to remember one username and complex password to access all their cloud-based systems, instead of multiple simpler passwords for each application. This single password must always be strong.
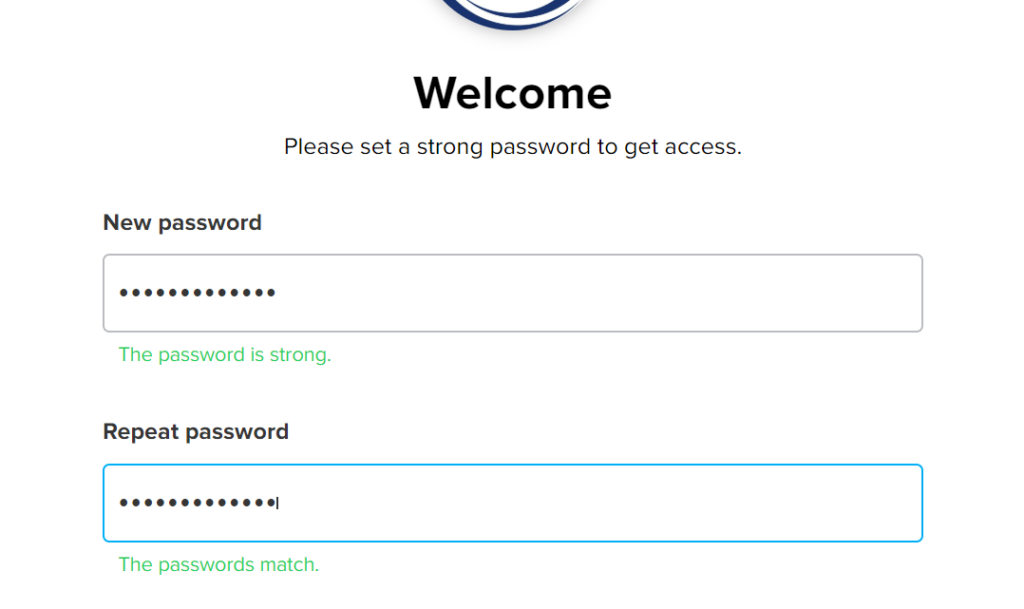
As a second layer of security, we also implement dual-authentication as standard which means that users will need to enter a code to access our systems. They will either receive this code via text message or they will need to generate one using an authentication app such as Google or Microsoft authenticator, where the code changes every 30 seconds.
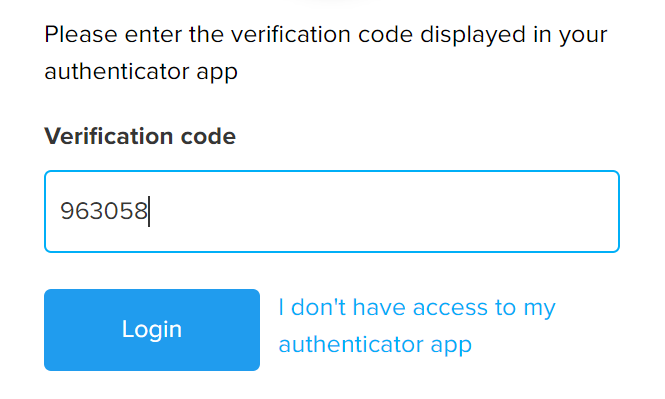
Therefore, unless a hacker can guess your username and strong password, steal your phone and guess the pin to access your phone, they will not be able to access your data.
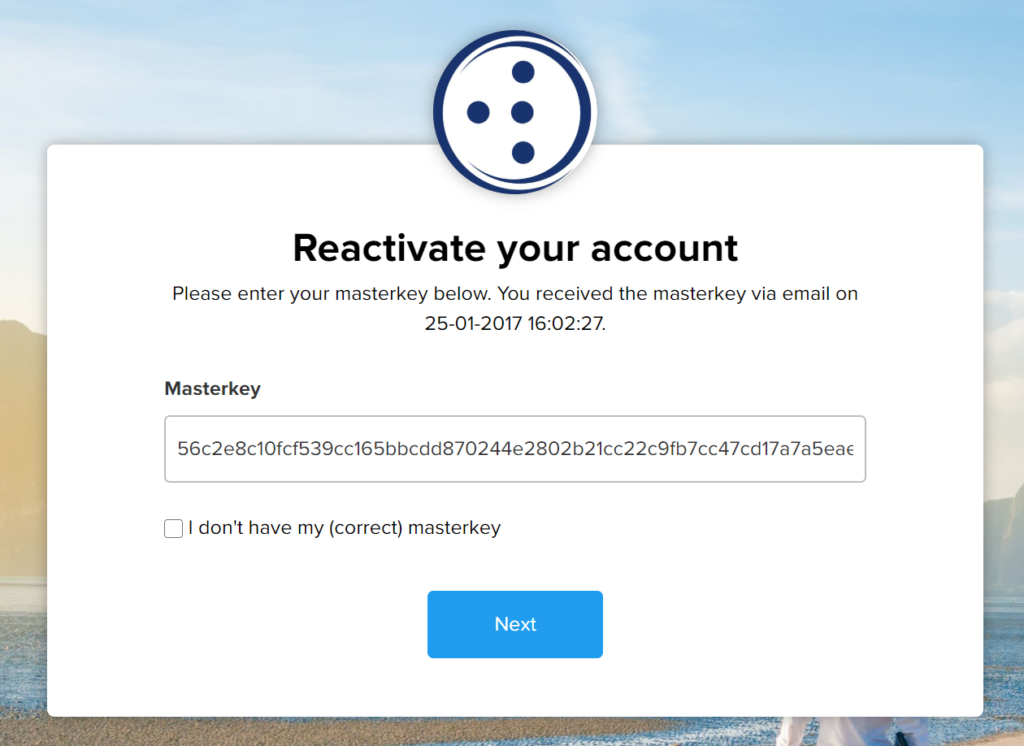
We can also set up schedules to change passwords at certain dates/intervals. Additionally, if you forget or need to change your password, you cannot do this without entering a masterkey. Some hackers may try to access your emails and then use a reset password wizard to access your systems. We nullify this as when you attempt to reset your password without using a complex masterkey, all the connections to your systems are automatically broken. This means even if they did manage to get into the system, nothing would work and only we would be able to reset the account once we had confirmed the user’s identity.
All of this means you can be confident that you can safely and securely access all of your systems.
2. Removing Users and Access:
Making sure your cloud apps are secure is not only about adding users but also removing them promptly when someone leaves. It is not uncommon when people leave an organisation that they wish to take certain lists of data or clients with them, so making sure people are removed as quickly as possible is crucial. As you can imagine, in large organisations where users come and go quite regularly this can be a thorny issue. If users are not removed, they could potentially be continuing to access your data if the administrator in your service provider does not remove their access.
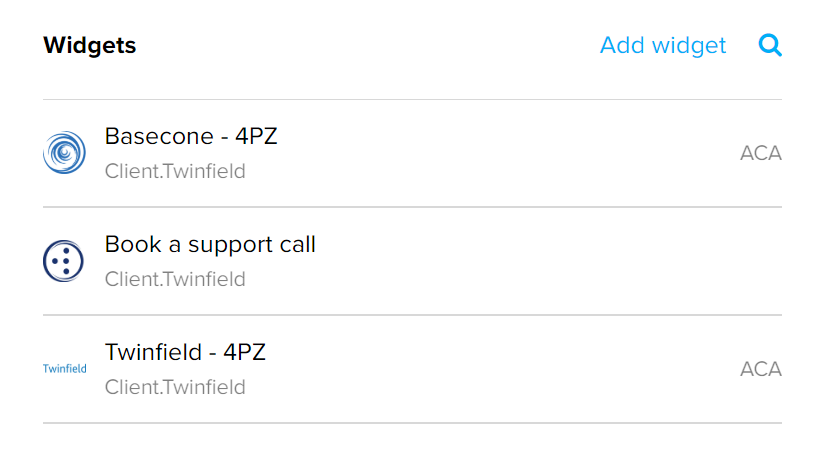
Since staff access their applications using a secure single sign-on, we are able to maintain the systems they access on their behalf. Where possible, a master administrator should set credentials on behalf of a user. This means that staff members might not necessarily know the credentials for any of the systems in your business so when they are blocked from the single sign-on platform, they are automatically blocked from accessing all other systems. If setting a password is maintained via the person’s email, i.e. the staff member must set it, you will get a list of the systems/widgets they can access via their profile which means you can simply remove the accounts from the systems in the list and nothing gets missed.
You can also control what systems users can and can’t see so your staff will not be able to access any information or functionalities which are not relevant to them or are sensitive in nature. If a client would like to be more hands-on in managing their user base, we even link the user to a company’s active directory of staff. This means that once they are removed from there, they are also removed from all our systems and apps automatically.
3. Group logins:
In some situations, and often to save on cost, some businesses will share a login to a system across multiple staff members. This can make it easy and cost-effective but is also less secure and compromises on audit trails and controls. Often when an individual leaves, the credentials are not amended (link to point 2 above). As we provide a single sign-on to each individual, the administrator could be the only person in the business who knows the actual system credentials and adds them to each user’s log-in widget. This does place a lot of emphasis on the administrator but, as a business owner, as long as you set effective controls on this individual such as a secure cloud location in which to store shared logins, this means you will have a safe list of items to change and update across the company should your administrator leave. This means you can stay secure whilst also remaining cost-effective, even though your provider would rather you weren’t.
At 4PointZero, we have various techniques and tools to assist businesses and accountants access their cloud systems securely so they are all protected. As businesses resell or purchase more and more apps it is becoming an increasingly risky area and thus it is very important to ensure you have correct controls in place to keep your clients and data secure. If you would like to know more, please get in contact with us at www.4pointzero.co.uk.
Frequently Asked Questions (FAQ)
Why is cloud accounting security important?
Cloud accounting security is crucial because it safeguards sensitive financial information from unauthorized access, cyberattacks, and data breaches. With businesses relying on cloud-based accounting systems, ensuring the security of this data is essential to maintain trust and compliance.
How does encryption enhance cloud accounting security?
Encryption involves converting data into a code to prevent unauthorized access. Cloud accounting platforms use encryption to protect data both during transmission and while stored on servers, making it extremely difficult for hackers to decipher sensitive information.
How do cloud accounting services protect data?
Cloud accounting services employ various security measures, including encryption, multi-factor authentication, regular security updates, and advanced firewalls. These measures work together to prevent unauthorized access and ensure data confidentiality.
Can I trust the security of cloud accounting software?
Reputable cloud accounting software providers invest heavily in security infrastructure and practices. Before choosing a software provider, it’s essential to research their security certifications, data protection policies, and user reviews to assess their reliability.
Are there any best practices for maintaining cloud accounting security?
Yes, best practices include regularly updating passwords, educating employees about security protocols, monitoring account activity for anomalies, keeping software up-to-date, and performing regular security audits.
What is multi-factor authentication (MFA), and why is it crucial?
Multi-factor authentication requires users to provide multiple forms of verification, such as a password and a unique code sent to their phone, before accessing their accounts. MFA adds an extra layer of security, reducing the risk of unauthorized access.



